| See Also |
| Contents |
| Setting up the Ground |
| Well, it seems people are getting crazy about Android platform(everyone is trying to buy an Android phone!). I don�t have an Android cell phone but, lets see if I can get my hands dirty with this Linux+java clean room engineered platform. To begin our journey we need Android SDK, a target to test with and the necessary tools. You can download the necessary file from these locations: Android SDK: http://developer.Android.com/sdk/index.html Deurus Android crackme 03: http://crackmes.de/users/deurus/android_crackme03/ Smali and baksmali: http://code.google.com/p/smali/ Dex2jar: http://code.google.com/p/dex2jar/ Java decompiler: http://java.decompiler.free.fr/ Download and install Android SDK, SDK platform(latest is 2.2 at the time of writing), necessary Java packages and rest of the tools. Create a virtual device from SDK menu and start emulation. Within few minutes you can see the emulator booting up and showing the phone screen. Well, thats it! we have our emulator up and running. |
| Getting Started with the Game |
| Now we need to install the software(crackme, its legal!) to the emulator. For that you may have to get acquainted with Android debug bridge(adb). Installing a apk file is pretty simple, all you have to do is to run two commands from Android SDK directory/tools. |
 |
| After the installation you can see the crackme icon from application menu. |
 |
| Now run the crackme by clicking on it. If everything went as expected you will see the crackme application on the screen. |
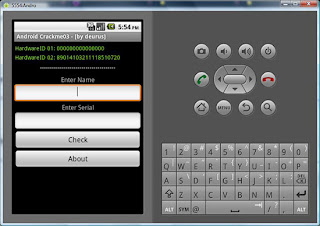 |
| Now we will play with it, pressing check button with no inputs pops a message 'Min 4 chars', and with a proper name it pops up 'Bad boy'. We have to remember these strings because we will be using them as our search keys when we disassemble the apk(actually dex) files. Also note that we have two hardware ids and we need to find out what those exactly means. |
| Real Android Reversing |
| As our crackme is up and running in emulator, we now move onto reversing it. If you have read apk file format, you can visualize it as a extended JAR file which essentially is a zip file. Now you can change the crackme file name fromCrackme03.apk to Crackme03.zip and decompress it to any folder. |
 |
| Now the interesting file for us is classes.dex, which contains the compiled vm codes. We are going to disassemble the dex file with baksmali. Commands are pretty simple as you can see from screen shots. |
 |
| If everything worked fine, we will have a folder structure similar to Java packages. Interesting .smali files are located at '\com\example\helloandroid'. Open all the .smali files into your favorite text editor(I use Notepad++). If you have never done anything related to reverse engineering/esoteric programming/assembly(IL) programming, you will probably think: WTF!. Relax. We have just opened a disassembled dex file. Now, if you are thinking how on earth someone can find the correct location of checking function, I hope you remember those pop up strings I told earlier. Yeah, 'Min 4 chars' and 'Bad boy'. Now we will use those strings as our search keys. Searching �Min 4 chars� in all the opened .smali files, we will find a hit in HelloAndroid$2.smali line 130. |
 |
| Our aim is to understand the serial checking function and write a keygen for it. For that we have to know all the dalvik opcodes that are used here. You can visit this page to understand the opcodes and after that you can convert disassembled code to much higher language constructs. I will provide a brief code snippet which actually implements the algorithm. Two hardware ids used are IMEI and sim serial number. |
| 01 //Read name from text box 02 const v23, 0x7f050004 03 invoke-virtual/range {v22 .. v23}, Lcom/example/helloandroid/HelloAndroid;->findViewById(I)Landroid/view/View; 04 move-result-object v9 05 06 //Read serial from text box 07 const v23, 0x7f050006 08 invoke-virtual/range {v22 .. v23}, Lcom/example/helloandroid/HelloAndroid;->findViewById(I)Landroid/view/View; 09 move-result-object v21 10 11 //Checking whether the name is of length greate than 4 12 const/16 v22, 0x4 13 move v0, v11 14 move/from16 v1, v22 15 if-ge v0, v1, :cond_51 16 17 //Popup showing Min 4 chars 18 const-string v23, "Min 4 chars" 19 const/16 v24, 0x1 20 .line 86 21 invoke-static/range {v22 .. v24}, Landroid/widget/Toast;->makeText(Landroid/content/Context;Ljava/lang/CharSequence;I)Landroid/widget/Toast; 22 move-result-object v13 23 .line 88 24 .local v13, notificacionToast:Landroid/widget/Toast; 25 invoke-virtual {v13}, Landroid/widget/Toast;->show()V 26 27 //There is a little exception trick to make integer string from username 28 //It converts aaaa to 97979797 which is ascii equivalent 29 invoke-virtual {v10, v5}, Ljava/lang/String;->charAt(I)C 30 move-result v3 31 32 //Getting first 5 chars from ascii converted name 33 const/16 v22, 0x0 34 const/16 v23, 0x5 35 move-object v0, v12 36 move/from16 v1, v22 37 move/from16 v2, v23 38 invoke-virtual {v0, v1, v2}, Ljava/lang/String;->substring(II)Ljava/lang/String; 39 40 //Converting it into integer abd xoring with 0x6B016 - Serial part 1 41 invoke-static {v12}, Ljava/lang/Integer;->parseInt(Ljava/lang/String;)I 42 move-result v22 43 const v23, 0x6b016 44 xor-int v22, v22, v23 45 46 //Getting IMEI from TelephonyManager 47 //http://developer.Android.com/reference/Android/telephony/TelephonyManager.html 48 invoke-virtual {v8}, Landroid/telephony/TelephonyManager;->getDeviceId()Ljava/lang/String; 49 move-result-object v6 50 .line 102 51 .local v6, imei2:Ljava/lang/String; 52 53 //Getting sim serial 54 invoke-virtual {v8}, Landroid/telephony/TelephonyManager;->getSimSerialNumber()Ljava/lang/String; 55 move-result-object v16 56 .line 103 57 .local v16, simsn:Ljava/lang/String; 58 59 //Getting first 6 chars from IMEI, and similarly from sim serial (IMEI.Substring(0,6) will be used as Serial part 3) 60 const/16 v22, 0x0 61 const/16 v23, 0x6 62 move-object v0, v6 63 move/from16 v1, v22 64 move/from16 v2, v23 65 invoke-virtual {v0, v1, v2}, Ljava/lang/String;->substring(II)Ljava/lang/String; 66 67 //Converting them to integer and xoring - Serial part2 68 invoke-static/range {v19 .. v19}, Ljava/lang/Integer;->parseInt(Ljava/lang/String;)I 69 move-result v22 70 invoke-static/range {v20 .. v20}, Ljava/lang/Integer;->parseInt(Ljava/lang/String;)I 71 move-result v23 72 xor-int v22, v22, v23 73 74 //Making a new StringBuilder object and formatting the string to part1-part2-part3 75 new-instance v22, Ljava/lang/StringBuilder; 76 invoke-static {v12}, Ljava/lang/String;->valueOf(Ljava/lang/Object;)Ljava/lang/String; 77 move-result-object v23 78 invoke-direct/range {v22 .. v23}, Ljava/lang/StringBuilder;-><init>(Ljava/lang/String;)V 79 const-string v23, "-" 80 invoke-virtual/range {v22 .. v23}, Ljava/lang/StringBuilder;->append(Ljava/lang/String;)Ljava/lang/StringBuilder; 81 move-result-object v22 82 invoke-static/range {v17 .. v18}, Ljava/lang/String;->valueOf(J)Ljava/lang/String; 83 move-result-object v23 84 invoke-virtual/range {v22 .. v23}, Ljava/lang/StringBuilder;->append(Ljava/lang/String;)Ljava/lang/StringBuilder; 85 move-result-object v22 86 const-string v23, "-" 87 invoke-virtual/range {v22 .. v23}, Ljava/lang/StringBuilder;->append(Ljava/lang/String;)Ljava/lang/StringBuilder; 88 move-result-object v22 89 move-object/from16 v0, v22 90 move-object/from16 v1, v19 91 invoke-virtual {v0, v1}, Ljava/lang/StringBuilder;->append(Ljava/lang/String;)Ljava/lang/StringBuilder; 92 move-result-object v22 93 94 //Checking whether user entered serial and program made serials are equal. 95 invoke-virtual {v14, v15}, Ljava/lang/String;->equals(Ljava/lang/Object;) |
| As you can see, the algorithm is pretty straight forward. It is using name and two hardware ids as input and doing some operations on them to make a serial. We can easily recode it in any programming language we prefer to make it as a keygen. Anyway, I am not posting any keygen sources as it will spoil the whole phun! |
| Decoding the Algorithm |
| A demonstrative serial calculation routine is given below: |
| Name: aaaaa HW ID1: 0000000000000000 HW ID2: 89014103211118510720 |
| Here are stepwise instructions on generating final serial number |
|
| Final Verification of Reversing |
| Now we will put the same magic number into our Crackme application. |
 |
| Bingo! everything worked as expected. Now, for all those who thinks it is pretty hard to read all those disassembled instructions and manually converting them to higher language constructs, there are other options. As dalvik is based on design of Java, it is also susceptible to decompilation. There is no decompiler available at this moment, but there is hope. For now we can use another utility which converts dex files to jar files so that we can use Java decompilers to see much more abstracted code. From starting of this blog post you may have noticed the tool dex2jar. Use dex2jar to convert classes.dex to classes.dex.dex2jar.jar. Open it in a Java decompiler and you can see much better output than dalvik disassembly. Please note that dex2jar is still in development phase and the output is meaningless at many places. This should be used only to get a quick understanding of all the functions. |
| Conclusion |
| In this introductory article, Dhanesh explains reversing Andriod using the emulator and all available tools in sequence with pictorial elaborative steps. It is mainly based to set up your ground for further reversing work on Andriod Platform. |
| Well, thats it! We have analyzed an Android program and defeated its protection. Cheerio! |
| See Also |
0 件のコメント:
コメントを投稿